The Role of Software Testing in Cyber Security

With the growing amount of cyberattacks, it is more important than ever for businesses to invest in cybersecurity. It seems like a huge breach is reported somewhere online or offline almost every day. This can result in hackers compromising and stealing millions or billions of data points. According to the data, roughly $5.2 trillion in value would be put at risk due to cyberattacks between 2019 and 2023. Furthermore, these breaches are costly and time-consuming to repair.
As hacking operations have reached dangerous levels, cybersecurity has become a major concern. Cybercriminals are known to use cutting-edge technology to assault digital networks in order to steal critical data from businesses.
The correct application of software testing measures is regarded as critical to limiting hacking events. This procedure has grown in popularity in recent years, and software testing has emerged as a reliable defense against cyber threats.
Security Testing
Security testing is a sort of software testing that identifies system vulnerabilities and ensures that the system’s data and resources are secure from potential invaders. It assures that the software system and application are free of hazards or risks that could result in a loss. Security testing of any system is focused on identifying all potential flaws and weaknesses in the system that could result in the loss of information or the organization’s reputation.
Types of Security Testing
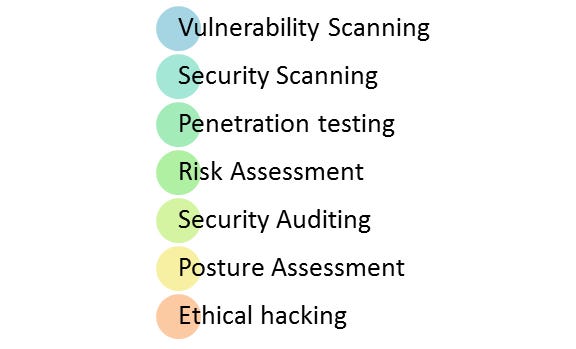
According to the Open Source Security Testing methodology document, there are seven primary forms of security testing. They are explained below:
- Vulnerability Scanning: This is done by scanning a system against known vulnerability signatures using automated tools.
- Security scanning entails discovering network and system flaws and then providing ways to mitigate these threats. This scanning can be done both manually and automatically.
- Penetration testing: This replicates a malicious hacker’s attack. This testing entails analyzing a specific system for potential vulnerabilities to an external hacking effort.
- Risk Assessment: This assessment entails an examination of the organization’s security risks. There are three levels of risk: low, medium, and high. This testing suggests risk-reduction controls and procedures.
- Security auditing is an internal check for security issues in applications and operating systems. An audit can also be performed by inspecting code line by line.
- Ethical hacking is the practice of breaking into an organization’s software systems. Unlike criminal hackers who steal for personal benefit, the goal is to uncover system security problems.
- Posture Assessment: This combines security scanning, ethical hacking, and risk assessments to demonstrate an organization’s entire security posture.
Security Testing Techniques

The following approaches are used in security testing:
- White Box: Tiger Box hacking is typically performed on a laptop that contains a collection of operating systems and hacking tools. This testing assists penetration testers and security testers in assessing vulnerabilities and conducting attacks.
- Black Box: The tester is authorized to test the network topology and technologies in its entirety.
- Grey Box: A mix of the white and black box models, it provides the tester with some knowledge about the system.
Why Software Testing Important
Software security is a crucial technique to help software withstand attacks throughout time and remain stable.
Software security is beneficial:
- Saving time and money on system restoration procedures
- Avoid the loss of client information and trust
- Avoid business interruptions and revenue loss
We will now examine the importance of security testing in software development by looking at the tests that can be performed to eliminate known vulnerabilities.
Security testing & Its Impact on Cyber Security
According to several statistics, over 3/4th of cyber attacks arise as a result of an unsecured application that incorporates unsafe code. Because applications are increasingly being outsourced to the worldwide population, they have become great targets for cyber-attacks. As a result, it is critical for a company to ensure the quality of the source code that links to the application. Such vulnerabilities can be smartly avoided with proper penetration testing implementation.
A penetration test, often known as a pen test, is a simulated cyber attack on your system with the goal of exploiting critical vulnerabilities. When it comes to web application security, penetration testing is useful for escalating a web application firewall (WAF).
Penetration testing is a cleverly planned system for analyzing security prior to a hacker’s attempt. Only by using penetration testing tools can one accurately reproduce genuine cyber attacks in order to identify security flaws.
If it can detect weak links within the software, the possibilities of safeguarding records, personal credentials, cardholder data, and so on are significantly boosted. To be more specific, penetration testing makes advantage of security flaws to build an effective defense strategy and prevent future cyber attacks.
A penetration test is also significant in network security. You can quickly identify potential security weaknesses using a dynamic approach to these testing. Furthermore, information on security compliance, security team reaction time, and so on can be obtained.
References
https://www.cyberdb.co/how-software-testing-is-incorporated-into-cyber-security/
https://study.com/academy/lesson/the-role-of-software-testing-in-cybercrime.html
https://www.geeksforgeeks.org/software-testing-security-testing/
https://impactqa.medium.com/what-is-the-role-of-software-testing-in-cyber-security-b539dae2feae
